Chris Sereno
I am making significant changes to this site. Thank you for your patience.
I no longer have a need for the Cisco Meraki MX64. It was only used for testing. It is in working condition. It has been reset to defaults and is unclaimed. It comes in the original box with the power and network cable. See the listing here.
We spend a lot of time monitoring our internal networks. Obviously, this is where we have the most tools at our disposal and where our actual responsibility lies. But, to provide good service to our customers and/or end users we also need to be aware of what is happening at our Internet providers and above. If you have global services then I recommend you monitor the submarine cables as well. For example, this was the latest submarine cable damage that impacted regions in Africa.
Performance and security is always a balancing act, but in the case of DNSSec it’s a no-brainer. In short, DNSSec allows a client to trust the domain owner when performing DNS queries. It’s another step to defending your domain (and subsequently your content and network) from the bad guys. An added benefit is there is no noticeable impact to performance!
CloudFlare just released a great blog post on their DNSSec offerings and how they are expanding.
So, all credit goes to Colm MacCárthaigh for this one. I think his recent post on Shuffle Sharding is so go it deserves a share and a place on my blog to serve as a reminder for me from time-to-time. This is one way AWS achieves the level of reliability and stability it has for its customers. Some of the methodology can easily be applied to traditional and on-prem infrastructure though as well.
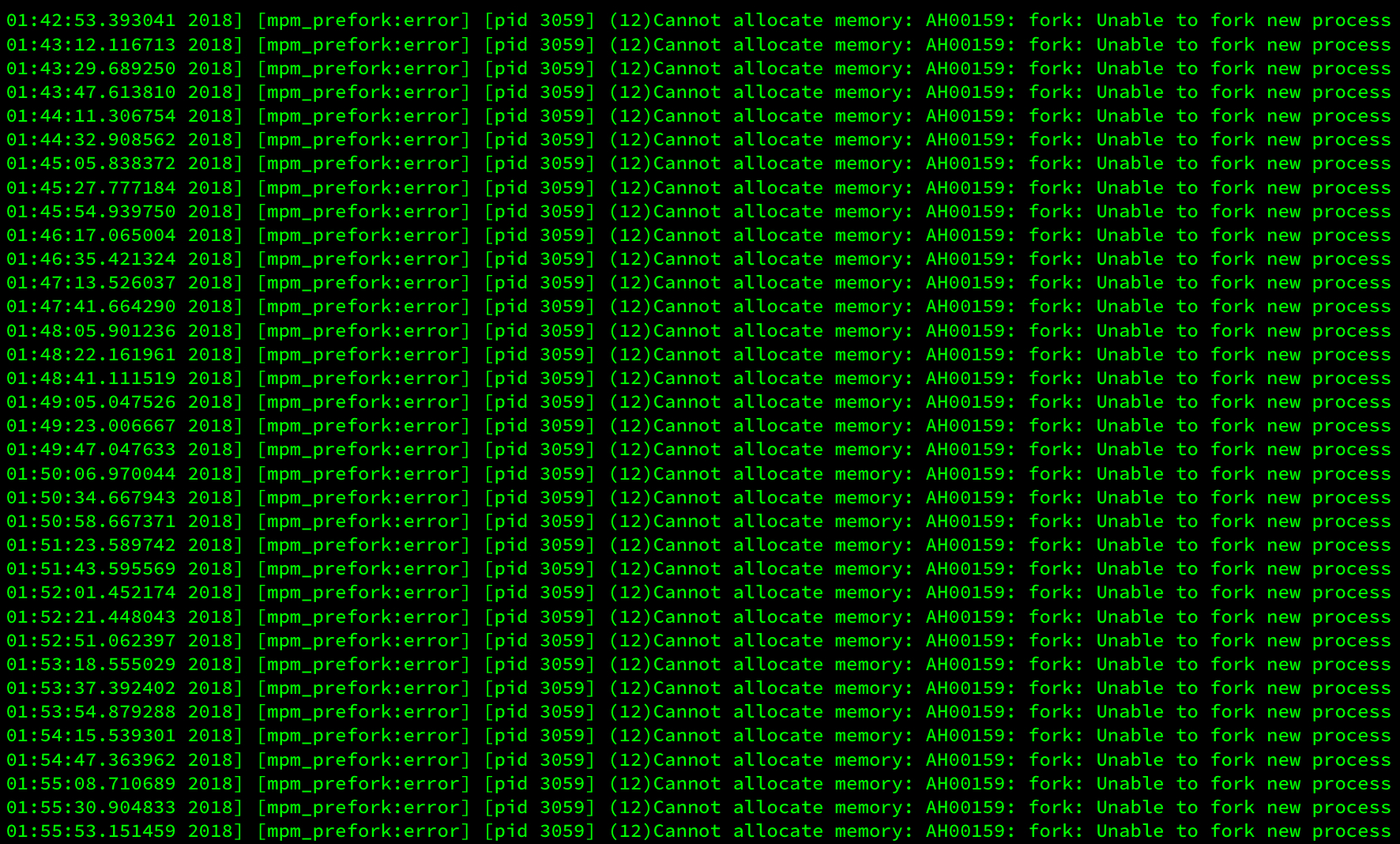
Symptoms Website randomly goes down a few times a week
Server stopped responding
Network and CPU logs show a small spike, but not enough to lock up a server
Stopping and starting the server resolves the problem
Details This pattern repeated several weeks until the customer grew tired of rebooting the server. The evidence did not seem to lead to a system issue or network or security security problem such as a denial of service.
Did you know you have a public Amazon profile that is automatically created when you sign up for an Amazon account? This profile doesn’t provide too much information publicly by default, but it is another data point for 3rd parties. Michael Bazzell from Intel Techniques provided a quick guide in his latest email newsletter on how to take a few easy steps to secure your Amazon profile.
The following is an excerpt taken from his email, and is intended only for a quick reference.
 Chris Sereno
Chris Sereno